Scam Briefs VoIume. I By: Darryl stephens & Najha Treadwell
Contents 1. THE THREAT OF AI VOICE CLONING 2.THE THREAT OF DEEP FAKE VIDEOS 3.THE THREAT OF “TOO GOOD TO BE TRUE” INVESTMENT SCAMS 4.THE THREAT OF DEFI RUG PULLS 5.THE THREAT OF CRYPTO DRAINER TACTICS 6.THE THREAT OF CRYPTO ADDRESS SPOOFING 7.THE THREAT OF CRYPTO SPAM DUSTING 8.THE THREAT OF CRYPTO FALSE GIVEAWAY SCAMS 9.THE THREAT OF CRYPTO PIG BUTCHERING 10.REFERENCE LIST
THE THREAT OF AI VOICE CLONING December 12th 2025 OVERVIEW Financial fraud and scams continue to escalate, with the Global Anti-Scam Alliance (GASA) reporting staggering losses of over $1.03 trillion in 2024. The primary goal of these criminal schemes remains the same: to steal your money or personal information. Among the latest and most sophisticatedthreats emerging in 2025 are AI-powered scams, with voice cloning being a critical concern. Scammers are now leveraging artificial intelligence to generate or alter voices for use in phone calls and videos. This technology is becoming so advanced that it can even mimic real accents, making the deception highly convincing. KEY EXAMPLE USED IN AI VOICE CLONING SCAMS: Family Emergency Deception (Grandparent Scams): A more direct and emotionally manipulative tactic involves cloning the voice of a friend or relative after obtaining a sample from social media videos. The scammer will call the victim, pretend to be the person, and claim they need money immediately for an emergency, such as ransom or bail. These are often referred to as "grandparent scams" because they frequently target older victims by posing as a grandchild in distress. Celebrity Impersonation: Fraudsters clone the voices of celebrities (like Elon Musk or Donald Trump, as noted in other scam types) to promote fake offers. They may use deepfake robocalls or videos to ask for donations to fraudulent causes, recommend fake investments, or announce a false giveaway. PROTECTIVE MEASURES: To protect yourself and investigate potential AI scams, consider the following actions:; Verify Identities (IDs): Always verify the identity of the person or entity contacting you. Research Online: Check the domains or company name involved and search for "company + scam or review" to see if others have reported fraudulent activity. Check Websites: Be vigilant for any imposter websites that may be attempting to mimic legitimate services. Monitor Transactions: Trace any suspicious transactions to see if funds are coming from or being sent to high- risk exchanges. REAL-LIFE EXAMPLE: Jennifer DeStefano directly experienced this threat when a scammer used an AI-cloned voice of her daughter during a call, falsely claiming the daughter had been kidnapped and demanding a ransom. This incident highlights how criminals are createweaponizing voice cloning to emotionally charged, urgent situations to trick victims into sending money. https://www.cnn.com/2023/04/29/us/ai-scamcalls-kidnapping-cec/index.html CONCLUSION AI voice cloning represents a rapidly growing threat in the landscape of digital fraud. As technology advances, the line between authentic and synthetic communication continues to blur. Awareness, verification, and vigilance are essential defenses against these evolving scams. Organizations and individuals must stay informed, adopt verification protocols, and educate others to reduce the risk of falling victim to AI-driven deception.
THE THREAT OF DEEPFAKE VIDEOS December 26th 2025 OVERVIEW PROTECTIVE MEASURES: Financial fraud and scams continue to escalate, with the Global Anti-Scam Alliance (GASA) reporting staggering losses of over $1.03 trillion in 2024. The primary goal of these criminal schemes remains the same: to steal your money or personal information.1 To protect yourself and investigate potential AI scams, consider the following actions: Be Aware of Red Flags: Look and listen for inconsistencies that might indicate a deepfake, such as: Unnatural facial movements, robotic gestures, or poor lip-syncing in videos. Inconsistent lighting or shadows, or mismatched skin tones. Lack of blinking or strange blinking patterns. Audio quality mismatches or unnatural speech patterns/tones. Difficulty showing a side profile during a live video call. Limit Your Digital Footprint: Be mindful of the images and videos you share publicly on social media, as this content feeds the AI models used to create deepfakes. Tighten privacy settings on all online accounts. Among the latest and most sophisticated threats emerging in 2025 are AI-powered scams, with deepfake videos being a critical concern. Deepfake video technology involves AI-generated videos, deepfake recordings, or real-time face- and body-swapping tools to create highly convincing and deceptive content. This technology can trick victims into thinking they are interacting with or viewing someone else. KEY EXAMPLE USED IN AI VOICE CLONING SCAMS: Promoting Fraudulent Schemes: Scammers create AIgenerated videos to promote fake products, services, or investments. Celebrity Impersonation: Fraudsters use deepfake videos and robocalls to impersonate public figures (like Elon Musk or Donald Trump) to promote fake investment opportunities, solicit donations, or announce fraudulent giveaways. REAL-LIFE EXAMPLE: YouTube creators directly experienced this threat when phishers used an AI-generated deepfake of CEO Neal Mohan. The fake video announced false changes to YouTube’s monetization policy, which was designed to trick creators into clicking malicious links or downloading malware. This incident highlights how criminals are weaponizing deepfake video technology to create deceptive corporate communications to steal credentials and compromise systems. https://incidentdatabase.ai/cite/965/ CONCLUSION The use of deepfake video technology is rapidly evolving to create emotionally charged, urgent situations, enabling criminals to weaponize technology to trick victims into sending money or sharing sensitive data. Organizations and individuals must stay informed, adopt verification protocols, and educate others to reduce the risk of falling victim to AI-driven deception.

THE THREAT OF “TOO GOOD TO BE TRUE” INVESTMENT SCAMS January 9th 2026 OVERVIEW Financial fraud and scams continue to escalate, with the Global Anti‑Scam Alliance (GASA) reporting staggering losses of over $1.03 trillion in 2024.The primary goal of these criminal schemes remains the same: to steal your money or personal information. Among the latest and most damaging threats emerging in 2025 are “too good to be true” investment scams, especially in the cryptocurrency space. Scammers pose as savvy “investment managers” and promise sky‑high, often “guaranteed” returns—if you just send them some crypto first. It’s classic social engineering, dressed up as a legitimate financial opportunity. KEY EXAMPLE USED IN “TOO GOOD TO BE TRUE” INVESTMENT SCAMS: Promises of sky‑high, low‑risk returns: The pitch centers on “guaranteed” or unusually high returns, sometimes framed as a special algorithm, insider strategy, or exclusive opportunity that you must fund with crypto to access. Unusual or changing payment methods: As the scam progresses, the scammer may request additional deposits, switch wallets, or add new payment methods (often crypto‑only) under the guise of “upgrading your account” or resolving technical issues. Up‑front crypto payments: Victims are told to send crypto first to “activate” the investment, cover “gas fees,” unlock higher returns, or pay supposed taxes or withdrawal fees before they can access their funds. PROTECTIVE MEASURES: To protect yourself and to investigate potential “too good to be true” investment scams, consider the following actions: Verify licensing and registration: Confirm that the investment firm, platform, or individual is properly licensed or registered with recognized regulators such as the SEC, FINRA, or your local financial authority before sending any funds. Refuse up‑front crypto payments for access or withdrawals: Legitimate investment firms do not require you to send new crypto just to “unlock” your existing balance, pay made‑up fees, or release your profits. REAL-LIFE EXAMPLE: Spark Capital advertised its "SPARK PPAP Wisdom System," an AI crypto trading software, with promises of making "testers" millionaires and delivering returns up to 2000%. After initial promises to fund accounts, the company pressured a victim to pay large up-front fees, starting at $5,000 and escalating to $50,000, for trading signals. The victim was ultimately unable to withdraw their transferred funds, and the company's website is now non-operational. https://www.excelliumltd.com/sparkppap-comreview-scam-exposed-report-for-refund/ CONCLUSION “Too good to be true” investment scams are a rapidly evolving threat in the crypto ecosystem, using professional-looking platforms and complex jargon to mask fraudulent intent. Scammers exploit trust, urgency, and the promise of unrealistic returns. Protection requires skepticism toward guaranteed profits, independent verification of any platform, and refusing to send crypto up front for access, fees, or withdrawals. Ongoing vigilance and education are essential defenses against these high-pressure schemes. https://www.excelliumltd.com/sparkppap-com-review-scam-exposed-report-for-refund/

THE THREAT OF DEFI RUG PULLS January 23, 2026 OVERVIEW Financial fraud and scams continue to escalate, with the Global Anti-Scam Alliance (GASA) reporting staggering losses of over $1.03 trillion in 2024. The primary goal of these criminal schemes remains the same: to steal your money or personal information. Among the latest and most damaging threats emerging in 2026 are DeFi rug pulls. This is a where growing form of cryptocurrency scam developers of a decentralized finance project suddenly withdraw all user funds and disappear, leaving investors with worthless tokens. KEY TACTICS USED IN DEFI RUG PULLS: Sudden Withdrawal ofUser Funds: Developers of a project (often a new token) secretly and suddenly drain all the cryptocurrency from the liquidity pool and vanish, making the invested tokens instantly worthless. Memecoin Exploitation: Rug pulls are increasingly shifting from DeFi protocols and NFT projects to predominantly memecoin-related schemes in 2025, exploiting the rapid hype and speculative nature of these tokens. Honeypot Tokens: Scams are becoming more complex, using malicious smart contracts known as "honeypot tokens" that prevent users from selling the tokens, ensuring only the scam developers can drain the funds. Evasion Tactics: Scammers use multi-wallet control strategies to hide the stolen funds and evade detection. PROTECTIVE MEASURES: To protect yourself and to investigate potential DeFi Rug Pull scams consider the following actions: Research the DeFi Project's Legitimacy: Thoroughly research the DeFi project or memecoin to ensure it is legitimate and not a newly created, unvetted scheme. Use reputable platforms for token purchases: The platform should clearly state its corporate structure, leadership,and security protocols. Trace Wallet Addresses: Use blockchain explorers or tracers to follow the flow of funds to see where crypto is being sent from or to, including identifying high-risk exchanges. REAL-LIFE EXAMPLE: Squid Game Token (SQUID, 2021): This token, inspired by the Netflix show, was marketed as a "play-to-earn" game. Its price soared from $0.01 to over $2,800, but investors soon found they were unable to sell their holdings. The developers then sold their own tokens, causing the price to plummet by 99% and resulting in a theft of over $3.38 million. https://www.trmlabs.com/resources/blog/squidgame-season-2-a-window-into-popular-cultureand-crypto-scams CONCLUSION DeFi rug pulls are a rapidly escalating threat in decentralized finance, exploiting a lack of central authority and fast transactions. Developers exploit the hype around new tokens and the complexity of smart contracts to instantaneously drain investor funds. Protecting against this requires independent verification of project legitimacy, extreme skepticism toward unvetted tokens, and vigilance for smart contract mechanisms that prevent selling.

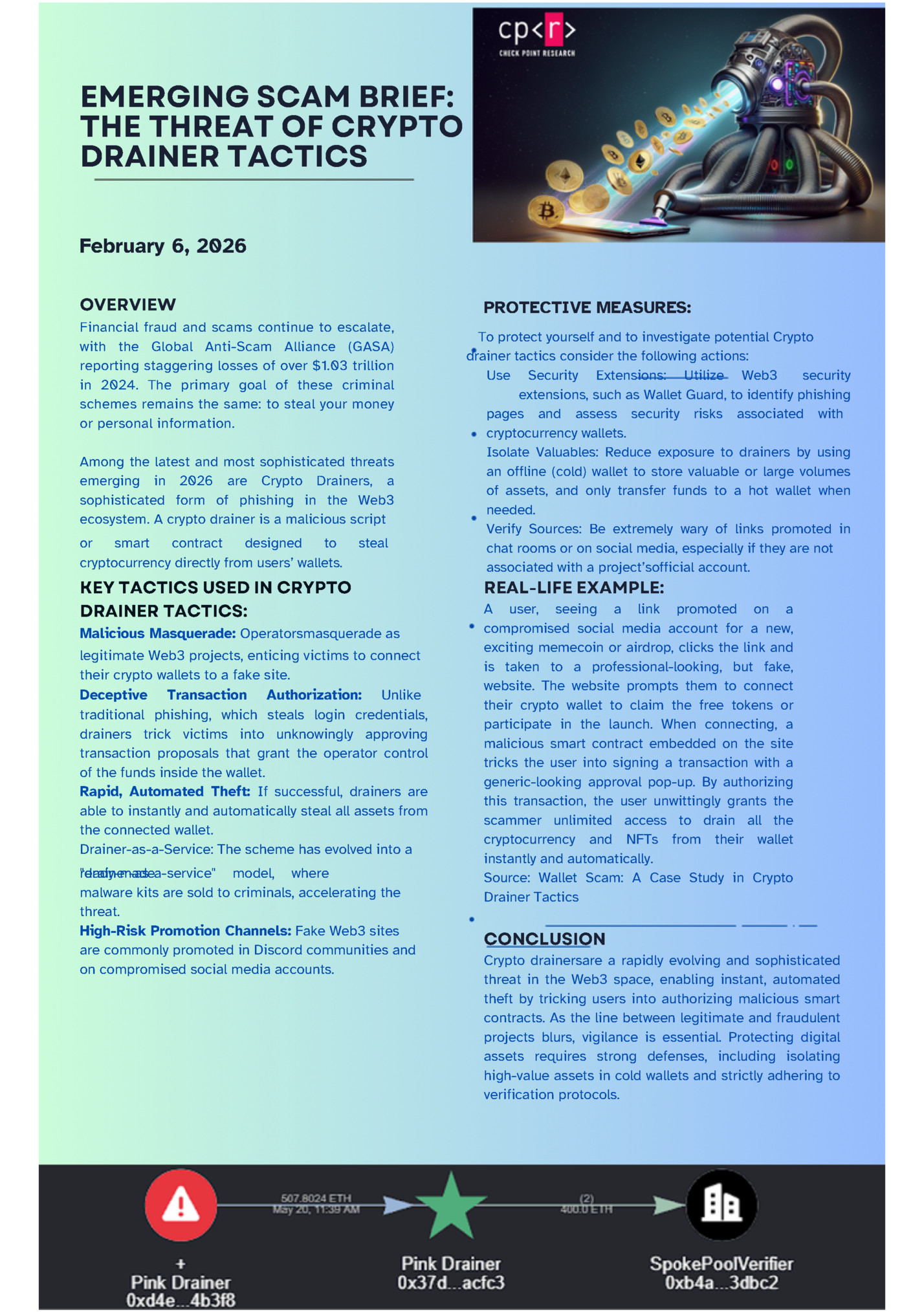
THE THREAT OF CRYPTO DRAINER TACTICS February 6, 2026 OVERVIEW PROTECTIVE MEASURES: Financial fraud and scams continue to escalate, with the Global Anti-Scam Alliance (GASA) reporting staggering losses of over $1.03 trillion in 2024. The primary goal of these criminal schemes remains the same: to steal your money or personal information. Among the latest and most sophisticated threats emerging in 2026 are Crypto Drainers, a sophisticated form of phishing in the Web3 ecosystem. A crypto drainer is a malicious script or smart contract designed to cryptocurrency directly from users’ wallets. steal KEY TACTICS USED IN CRYPTO DRAINER TACTICS: Malicious Masquerade: Operatorsmasquerade as legitimate Web3 projects, enticing victims to connect their crypto wallets to a fake site. Deceptive Transaction Authorization: Unlike traditional phishing, which steals login credentials, drainers trick victims into unknowingly approving transaction proposals that grant the operator control of the funds inside the wallet. Rapid, Automated Theft: If successful, drainers are able to instantly and automatically steal all assets from the connected wallet. Drainer-as-a-Service: The scheme has evolved into a "drainer-as-a-service" model, where ready-made malware kits are sold to criminals, accelerating the threat. High-Risk Promotion Channels: Fake Web3 sites are commonly promoted in Discord communities and on compromised social media accounts. To protect yourself and to investigate potential Crypto drainer tactics consider the following actions: Use Security Extensions: Utilize Web3 security extensions, such as Wallet Guard, to identify phishing pages and assess security risks associated with cryptocurrency wallets. Isolate Valuables: Reduce exposure to drainers by using an offline (cold) wallet to store valuable or large volumes of assets, and only transfer funds to a hot wallet when needed. Verify Sources: Be extremely wary of links promoted in chat rooms or on social media, especially if they are not associated with a project’sofficial account. REAL-LIFE EXAMPLE: A user, seeing a link promoted on a compromised social media account for a new, exciting memecoin or airdrop, clicks the link and is taken to a professional-looking, but fake, website. The website prompts them to connect their crypto wallet to claim the free tokens or participate in the launch. When connecting, a malicious smart contract embedded on the site tricks the user into signing a transaction with a generic-looking approval pop-up. By authorizing this transaction, the user unwittingly grants the scammer unlimited access to drain all the cryptocurrency and NFTs from their wallet instantly and automatically. Source: Wallet Scam: A Case Study in Crypto Drainer Tactics CONCLUSION Crypto drainersare a rapidly evolving and sophisticated threat in the Web3 space, enabling instant, automated theft by tricking users into authorizing malicious smart contracts. As the line between legitimate and fraudulent projects blurs, vigilance is essential. Protecting digital assets requires strong defenses, including isolating high-value assets in cold wallets and strictly adhering to verification protocols.
THE THREAT OF CRYPTO ADDRESS SPOOFING February 20, 2026 OVERVIEW In 2025, financial fraud continues to escalate, with global scam losses reaching $442 billion, according to Global Anti-Scams Alliance (GASA) and Feedzai. US businesses reported losing an average of 9.8% of their revenue to fraud, and crypto scams hit an estimated $17 billion in losses. The primary goal of these criminal schemes remains the same: to steal your money or personal information. Among the latest and most sophisticated threats emerging in 2025 is Crypto Address Spoofing, also known as Address Poisoning. This is a deceptive tactic where scammers trick victims into sending cryptocurrency to the wrong address by generating a malicious address that looks almost identical to one the victim has recently used. KEY TACTICS USED IN CRYPTO DRAINER TACTICS: Zero-Value Transactions: The scammer sends a token transaction with a zero or very small value from an address that has the first and last few characters matching the victim's legitimate, frequently used address. This transaction appears in the victim's wallet history.1 A "Familiar" Address: When the victim attempts a new transaction, they often copy a previous recipient's address from their transaction history for convenience. The victim inadvertently copies the scammer's spoofed address, believing it is the legitimate one. The "Look-Alike": The near-identical match of the starting and ending characters is designed to defeat a user's quick, visual check, exploiting the user's habit of only checking the first and last few characters of the long crypto address. PROTECTIVE MEASURES: Toprotect yourself and to investigate potential address spoofing scams consider the following actions: Always Verify the Full Address: Do not rely on checking only the first and last few characters. Copy the entire address and paste it into a reliable block explorer to confirm it is the correct, legitimate address.1 Use the Address Book Feature: Save and use the address book feature in your wallet or exchange for all frequently used addresses. Do not rely on manually copying from a transaction history.1 1.Send a Small Test Amount: For large or high-value transfers to a new address, send a minimal amount first to confirm the transaction is successful and the funds arrive at the intended destination before transferring the main amount. REAL-LIFE EXAMPLE: In May 2024, a crypto whale lost an estimated $68 million in wrapped Bitcoin (WBTC). They were the target of an address poisoning attack in which the attacker tricked them into sending crypto to the wrong address by poisoning their transaction history with malicious lookalike addresses. Once the targeted copy-pasted this address into a new transaction, their crypto was sent to the attacker instead of its intended recipient. https://www.halborn.com/blog/post/massive68million-address-poisoning-hackunderscores- ongoing-cyber-threat CONCLUSION Crypto Address Spoofing (Address Poisoning) is a sophisticated threat where scammers "poison" a wallet's transaction history with a look-alike address, tricking users into high-value transfers, such as the $68 million loss in May 2024. Protecting against this requires disciplined security practices: always verify the full address on a block explorer, use the address book feature, and send a small test amount before any major transfer. This vigilance is the last defense against a scam that preys on convenience.

THE THREAT OF CRYPTO SPAM DUSTING March 6, 2026 OVERVIEW In 2025, financial fraud continues to escalate, with global scam losses reaching $442 billion, according to Global Anti-Scams Alliance (GASA) and Feedzai. US businesses reported losing an average of 9.8% of their revenue to fraud, and crypto scams hit an estimated $17 billion in losses. The primary goal of these criminal schemes remains the same: to steal your money or personal information. Among the latest and most sophisticated threats emerging in 2025 is Spam Dusting, an attack where a minuscule amount of cryptocurrency, known as "dust," is sent to thousands of wallet addresses. The objective is not to steal the small amount of funds, but to de-anonymize the wallet for a future, more targeted attack, violating the user's privacy and potentially leading to larger financial losses. KEY TACTICS USED IN CRYPTO SPAM DUSTING: Mass Distribution: The scammer broadcasts "dust" (a tiny, virtually worthless amount of crypto) to a large number of public wallet addresses, often across popular blockchains. De-Anonymization: By tracking the subsequent movement of the "dusted" funds, attackers attempt to link multiple wallet addresses to a single entity, compromising the victim's privacy and creating a profile for a later attack. Targeted Phishing: Once a victim is deanonymized, the attacker can use the newly-linked information to conduct highly personalized and targeted phishing or social engineering attacks for greater sums. PROTECTIVE MEASURES: To protect yourself against potential spam dusting scams, consider the following actions: Ignore the Dust: Do not attempt to move, spend, or interact with the unsolicited "dust" transaction. Most modern wallets have features to hide these small, spam transactions. Use Wallet Features: Utilize crypto wallets that automatically flag or hide dusting transactions, making them effectively invisible and untraceable.1 Never Mix Funds: Avoid consolidating the "dusted" funds with other assets in your wallet, as this may inadvertently help the attacker track your total holdings and compromise your privacy. REAL-LIFE EXAMPLE: In late October 2018, the developers of the Samourai wallet, which stores Bitcoins, announced that some of its users were subject to a dusting attack. The company released a tweet warning its customers and explaining how to prevent such cases. In order to protect users from this type of attack, the wallets began to notify in real time when a dusting attack is taking place and, in addition, they created a tool called Do Not Spend that allows users to identify these suspicious balances and avoid using them in future transactions. https://www.binance.com/en/square/post/583843 CONCLUSION Spam Dusting is a privacy-violating threat where criminals use minuscule transactions to de-anonymize a crypto wallet's owner for a future, targeted attack. Protecting against this requires disciplined security practices: ignore the dust transaction, use wallet features that hide the dust, and never attempt to move or spend the unsolicited funds. This vigilance is the last defense against a scam that preys on transaction monitoring and user privacy.

Fleepit Digital © 2021